kmd wrote:is it enough for anything? im gonna now use vbox as primary vm.
Physical machine always better. However you can setup VM that will be protected from 99.9% of antivm tricks seen in ITW malware up to date. I'm not using VirtualBox as primary VM but I have it customized too. Few simple steps to configure VirtualBox.
1. Create new VM, install Windows. Do not install VM Tools/Additions <- this is important because even uninstalled they leave traces in registry and *.inf files on disk.
2. Configure VM DMI, see previous post, important options usually checked by malware:
Disk serial number, harddisk model number, BIOS related info, system vendor, motherboard vendor, chassis vendor. Settings to configure (assuming you use AHCI controller):
VBoxInternal/Devices/ahci/0/Config/Port0/ModelNumber
VBoxInternal/Devices/ahci/0/Config/Port0/SerialNumber
VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseDate
VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVendor
VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVersion
VBoxInternal/Devices/pcbios/0/Config/DmiSystemFamily
VBoxInternal/Devices/pcbios/0/Config/DmiSystemProduct
VBoxInternal/Devices/pcbios/0/Config/DmiSystemVendor
VBoxInternal/Devices/pcbios/0/Config/DmiBoardVendor
VBoxInternal/Devices/pcbios/0/Config/DmiBoardProduct
VBoxInternal/Devices/pcbios/0/Config/DmiChassisVendor
Put your own info in these fields, for example copy from your real machine (see msinfo32).
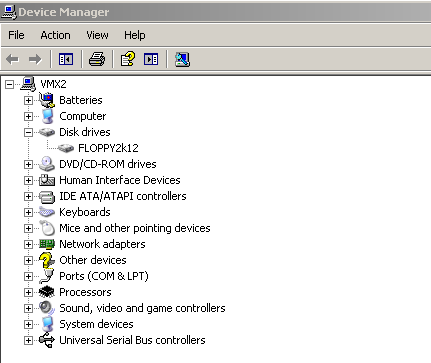
3. Replace Virtual Box environment dlls with attached. Note: they are for x64 VirtualBox v4.2.0.80737 and may not work with later/previous versions. Originally these dlls contains a lot of hardcoded data related to virtual machine devices, Video BIOS ID, ACPI table etc. This can be used to determine if we are running inside virtual machine or not, because Windows inside virtual machine uses this data and WMI of course takes this info into account. For example of such info see HKLM\HARDWARE\DESCRIPTION\System or Device Manager / MsInfo32 / DxDiag.
Dlls are patched to get rid of most important markers (including patched Video BIOS data). Since they are patched their digital signature become invalid. Do not worry, no viruses inside. Create backup copy of dlls for sure.
4. Create full VM copy with VM settings.
Now you can do whatever you want - install malware after then install tools/debuggers etc.