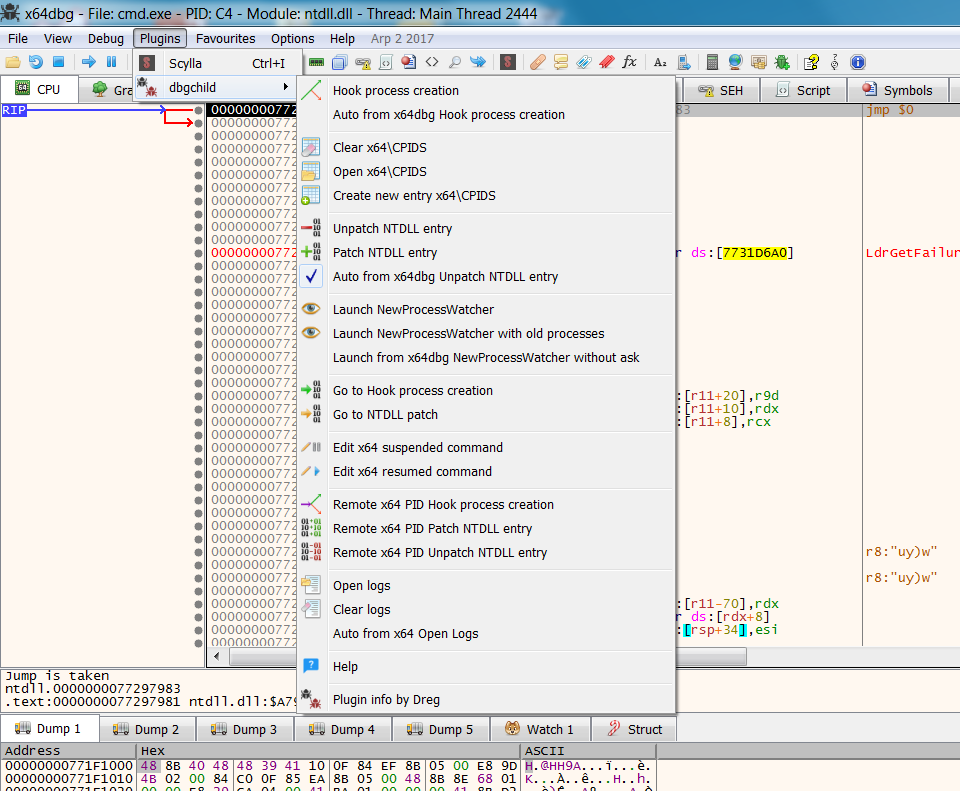
DbgChild is a stand alone tool for debugging child processes. DbgChild can be used in conjunction with a plugin for a debugger. Currently DbgChild supports a plugin for the x86/x64 x64dbg debugger.
https://github.com/David-Reguera-Garcia-Dreg/DbgChild
Features
These components are:
Also you can replace each component for your own specific component.
WARNING: The code is bullshit and there are some bugs, I know.
https://github.com/David-Reguera-Garcia-Dreg/DbgChild
Features
- Hook process creation for x86 or x64 child processes
Patching and unpatching of NTDLL process creation for x86 and x64 child processes
Process watcher for auto launching of new x64dbg instance when child process detected
Modify the suspend (pre) and resume (post) logic to adapt to your own requirements
These components are:
- CreateProcessPatch.exe - Hook ZwCreateUserProcess (two separate exe files for x86 and x64) and loads DbgChildHookDLL.dll
DbgChildHookDLL.dll - (two separate dll files for x86 and x64) - outputs process id's to CPIDS folder
NTDLLEntryPatch.exe - Patches or unpatches LdrInitializeThunk (two separate exe files for x86 and x64)
DbgChild.dp32 - x64dbg plugin x86
DbgChild.dp64 - x64dbg plugin x64
NewProcessWatcher.exe - Watches for new child processes from the CPIDS folder
x64_post.unicode.txt - Support file
x64_pre.unicode.txt - Support file
x86_post.unicode.txt - Support file
x86_pre.unicode.txt - Support file
Also you can replace each component for your own specific component.
WARNING: The code is bullshit and there are some bugs, I know.