Hello folks!
I'm glad to offer you a new version of Vba32 AntiRootkit 3.12.5.2 beta. Current build is 168.
Download link: http://anti-virus.by/en/beta.shtml
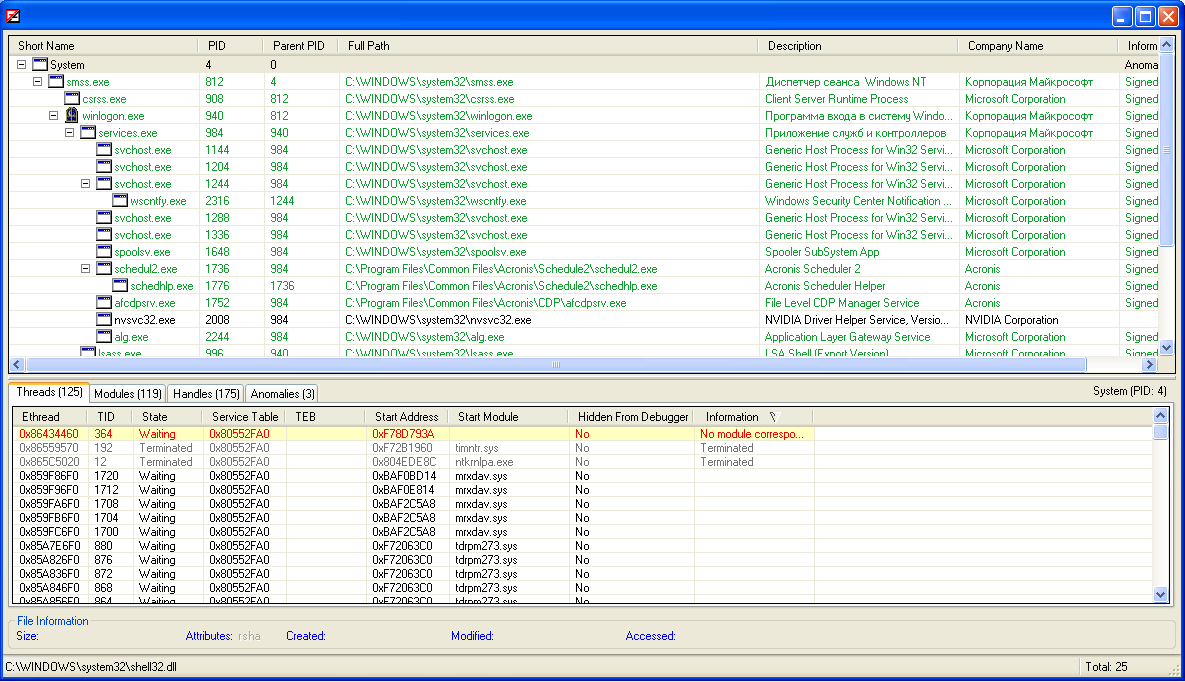
+ Process List window replaced with Process Manager. Significantly increased informative content
+ Listing anomalies for each process
+ Operations on processes ( Terminate, Terminate and Delete, Suspend / Resume, Dump )
+ Listing modules, including hidden
+ Operations on modules ( Unmap, Dump )
+ Listing threads, including hidden and anomaly
+ Operations on threads, including system threads ( Terminate, Suspend / Resume )
+ Listing handles
We've added possibility of full-fledged working with process list:
- process termination;
- process suspend and resume;
- process dump.
Process list can be displayed in treelike and list-oriented formats. You can receive there a great number of various helpful information: PID, EPROCESS address, PEB address, etc. All headers in the table are optional and you can choose only necessary settings.
Vba32 AntiRootkit detects hidden and anomaly processes too.
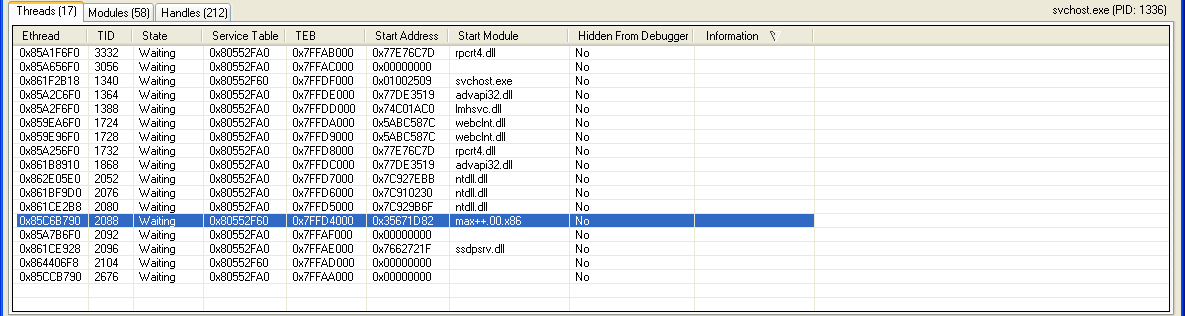
Thread list:
- thread termination;
- thread suspend and resume.
All headers in the list are optional.
Hidden and anomaly threads are detected.
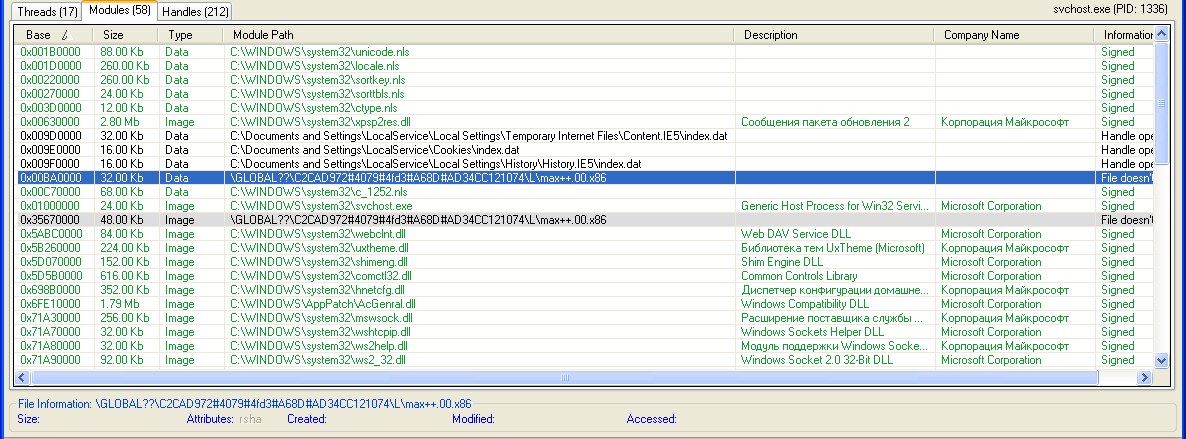
Module list:
- unmap in process;
- module dump.
Hidden and anomaly modules are detected.
Process Manager provides information about handles and interpretation of detected anomalies.
+ Listing unloaded kernel modules
These modules have Unloaded modules state.
+ Detection and restoration of hooks in IAT ( for kernel modules )
Frequently used method of hijacking.
+ View/delete for Lego, SeFileSystem, LastChanceShutdown, Shutdown, BugCheckReason, FsRegistrationChange notificators
It can be helpful.
+ Network Tool window ( parsing of host and lmhost files, persistent routes, LSP providers )
+ Dedicated antirootkit desktop
Very useful feature in the light of desktop blockers.
Attention: the feature is used with Vba32 Defender that blocks process and drivers loading.
+ Full safe-mode support
+ Detection of revoked certificates
Appearance of Stuxnet has revealed us that we can't unconditionally trust to digital signatures. But it works only in updated Windows or with Internet connection.
+ Increased the number of checked autorun items ( Print Provider, Control Panel objects, Known DLLs, URLSearch IE, Toolbar IE, IE Extensions, etc. )
+ Support of Windows 7 SP1
It's crucial issue.
* Search of hidden drivers was improved, added detection of numerous anomalies
* Increased low-level scanning speed
We have increased low-level speed about twice.
* Fixed BSOD on highly fragmented NTFS folumes
* "Don't display items digitally signed" option replaced with "Don't display trusted items"
* HTML-report was improved
* Internal caching of scanning files was improved
It has increased speed too.
* Help in Russian was improved
Known problems:
- Process Manager sometimes is hung. Don't scare :) It's happened not often. We are solving the problem;
- launching the antirootkit from dedicated desktop can lead to system deadlock on computers with some NVIDIA video card. It's happened not often too;
- audio sometimes is lost. It's connected with Vba32 Defender mode. We are going to solve this problem in the future.
You can send your suggestions, wishes, dumps and other helpful information to arkit@anti-virus.by.
And invite you to partcipate in beta testing.
I'm glad to offer you a new version of Vba32 AntiRootkit 3.12.5.2 beta. Current build is 168.
Download link: http://anti-virus.by/en/beta.shtml
+ Process List window replaced with Process Manager. Significantly increased informative content
+ Listing anomalies for each process
+ Operations on processes ( Terminate, Terminate and Delete, Suspend / Resume, Dump )
+ Listing modules, including hidden
+ Operations on modules ( Unmap, Dump )
+ Listing threads, including hidden and anomaly
+ Operations on threads, including system threads ( Terminate, Suspend / Resume )
+ Listing handles
We've added possibility of full-fledged working with process list:
- process termination;
- process suspend and resume;
- process dump.
Process list can be displayed in treelike and list-oriented formats. You can receive there a great number of various helpful information: PID, EPROCESS address, PEB address, etc. All headers in the table are optional and you can choose only necessary settings.
Vba32 AntiRootkit detects hidden and anomaly processes too.
Thread list:
- thread termination;
- thread suspend and resume.
All headers in the list are optional.
Hidden and anomaly threads are detected.
Module list:
- unmap in process;
- module dump.
Hidden and anomaly modules are detected.
Process Manager provides information about handles and interpretation of detected anomalies.
+ Listing unloaded kernel modules
These modules have Unloaded modules state.
+ Detection and restoration of hooks in IAT ( for kernel modules )
Frequently used method of hijacking.
+ View/delete for Lego, SeFileSystem, LastChanceShutdown, Shutdown, BugCheckReason, FsRegistrationChange notificators
It can be helpful.
+ Network Tool window ( parsing of host and lmhost files, persistent routes, LSP providers )
+ Dedicated antirootkit desktop
Very useful feature in the light of desktop blockers.
Attention: the feature is used with Vba32 Defender that blocks process and drivers loading.
+ Full safe-mode support
+ Detection of revoked certificates
Appearance of Stuxnet has revealed us that we can't unconditionally trust to digital signatures. But it works only in updated Windows or with Internet connection.
+ Increased the number of checked autorun items ( Print Provider, Control Panel objects, Known DLLs, URLSearch IE, Toolbar IE, IE Extensions, etc. )
+ Support of Windows 7 SP1
It's crucial issue.
* Search of hidden drivers was improved, added detection of numerous anomalies
* Increased low-level scanning speed
We have increased low-level speed about twice.
* Fixed BSOD on highly fragmented NTFS folumes
* "Don't display items digitally signed" option replaced with "Don't display trusted items"
* HTML-report was improved
* Internal caching of scanning files was improved
It has increased speed too.
* Help in Russian was improved
Known problems:
- Process Manager sometimes is hung. Don't scare :) It's happened not often. We are solving the problem;
- launching the antirootkit from dedicated desktop can lead to system deadlock on computers with some NVIDIA video card. It's happened not often too;
- audio sometimes is lost. It's connected with Vba32 Defender mode. We are going to solve this problem in the future.
You can send your suggestions, wishes, dumps and other helpful information to arkit@anti-virus.by.
And invite you to partcipate in beta testing.